doc attached
Lab 3
Introduction
Every company needs to take risks to thrive, but not too much risk which could be catastrophic. Finding the balanced amount of risk requires identifying what opportunities (or threats) are present, understanding how significant each of them is, recognizing what action to take to smartly handle both opportunities and risks, and lastly, monitoring all of the above, including discovering more prospects and threats. All told, this is called risk management. Specific to the seven domains of the IT infrastructure, this lab will cover IT risk management.
In this lab, you will define the purpose of an IT risk management plan, you will define the scope for an IT risk management plan that encompasses the seven domains of a typical IT infrastructure, you will relate the risks, threats, and vulnerabilities to the plan, and you will create an IT risk management plan outline that incorporates the five major parts of an IT risk management process.
Learning Objectives
Upon completing this lab, you will be able to:
Define the purpose and objectives of an IT risk management plan.
Define the scope and boundary for an IT risk management plan to encompass the seven domains of a typical IT infrastructure.
Relate identified risks, threats, and vulnerabilities to an IT risk management plan and risk areas.
Incorporate the five major parts of an IT risk management process into a risk management plan’s outline.
Craft an outline for an IT risk management plan, which includes the seven domains of a typical IT infrastructure and the five major parts of risk management and risk areas.
Deliverables
Upon completion of this lab, you are required to provide the following deliverables to your instructor:
Lab Report file;
Lab Assessment (worksheet or quiz - see instructor for guidance).
Note: This is a paper-based lab. To successfully complete the deliverables for this lab, you will need access to Microsoft® Word or another compatible word processor. For some labs, you may also need access to a graphics line drawing application, such as Visio or PowerPoint.
On your local computer, create a new document.
You will use this document as your Lab Report.
On your local computer, open a new web browser window.
Using your favorite search engine, search for information on the IT risk management process.
Briefly review at least five of the first page results.
In your browser, navigate to https://www.uvm.edu/sites/default/files/UVM-Risk-Management-and-Safety/Guide_to_Risk_Opportunity_Assessment_Response.pdf.
Review the PDF titled “Guide to Risk Assessment & Response.”
Note: Take special note of the University of Vermont’s “Guide to Risk Assessment & Response” document and the insightful sections titled “Things to Keep in Mind” and “Steps to Follow” for each of the assessment steps.
In your browser, navigate to https://web.archive.org/web/20130418005540/http://www.education.nt.gov.au/__data/assets/pdf_file/0011/4106/risk_management_process.pdf.
Review the PowerPoint slide deck titled “The Risk Management Process.”
In your Lab Report file, describe in what ways the risk management process in both IT and non-IT environments are similar. Briefly describe in your own words the five major steps of risk management: plan, identify, assess, respond, and monitor.
In your Lab Report file, describe the plan.
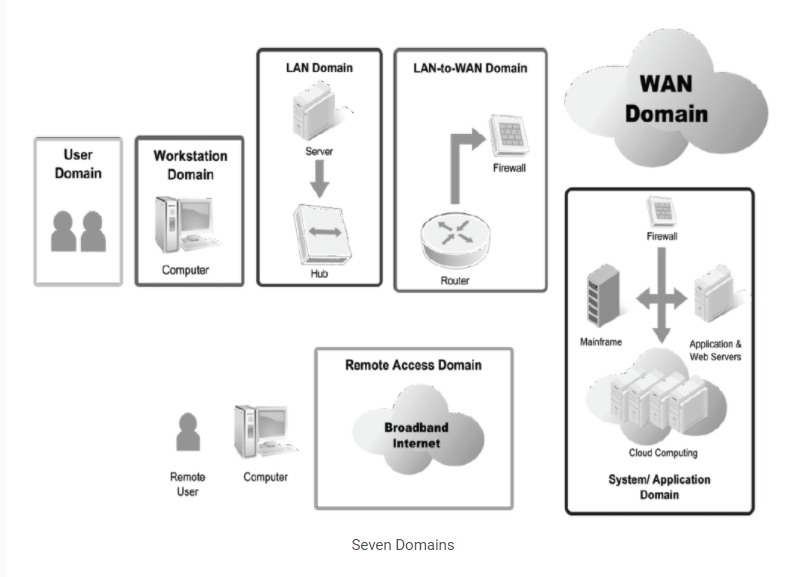
Review the seven domains of a typical IT infrastructure.
Seven Domains
Assume the following table of risks, threats, and vulnerabilities were found in a health care IT infrastructure servicing patients with life-threatening conditions. Review the risks in the table. Consider how you might manage each risk and which of the seven domains each one affects:
| Risks, Threats, and Vulnerabilities |
| Unauthorized access from public Internet |
| Hacker penetrates IT infrastructure and gains access to your internal network |
| Communication circuit outages |
| Workstation operating system (OS) has a known software vulnerability |
| Denial of service attack on organization’s e-mail |
| Remote communications from home office |
| Workstation browser has software vulnerability |
| Weak ingress/egress traffic-filtering degrades performance |
| Wireless Local Area Network (WLAN) access points are needed for Local Area Network (LAN) connectivity within a warehouse |
| Need to prevent rogue users from unauthorized WLAN access |
| User destroys data in application, deletes all files, and gains access to internal network |
| Fire destroys primary data center |
| Intraoffice employee romance gone bad |
| Loss of production data server |
| Unauthorized access to organization-owned workstations |
| LAN server OS has a known software vulnerability |
| User downloads an unknown e-mail attachment |
| Service provider has a major network outage |
| User inserts CDs and USB hard drives with personal photos, music, and videos on organization-owned computers |
| Virtual Private Network (VPN) tunneling between the remote computer and ingress/egress router |
In your Lab Report file, for each of the domains, create an outline in the scope of your risk management plan. Include the following topics—the five major parts of an IT risk management process—for each domain:
Risk planning
Risk identification
Risk assessment
Risk response
Risk monitoring
Note: This completes the lab. Close the web browser, if you have not already done so.



